Proof of knowledge
In cryptography, a proof of knowledge is an interactive proof in which the prover succeeds 'convincing' a verifier that the prover knows something. What it means for a machine to 'know something' is defined in terms of computation. A machine 'knows something', if this something can be computed, given the machine as an input. As the program of the prover does not necessarily spit out the knowledge itself (as is the case for zero-knowledge proofs[1]) a machine with a different program, called the knowledge extractor is introduced to capture this idea. We are mostly interested in what can be proven by polynomial time bounded machines. In this case the set of knowledge elements is limited to a set of witnesses of some language in NP.
Let  be a language element of language
be a language element of language  in NP, and
in NP, and  the set of witnesses for x that should be accepted in the proof. This allows us to define the following relation:
the set of witnesses for x that should be accepted in the proof. This allows us to define the following relation: 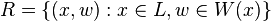 .
.
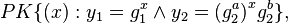
A proof of knowledge for relation  with knowledge error
with knowledge error  is a two
party protocol with a prover
is a two
party protocol with a prover  and a verifier
and a verifier  with the following two properties:
with the following two properties:
- Completeness: if
 , the prover P who knows witness
, the prover P who knows witness  for
for  succeeds in convincing the verifier
succeeds in convincing the verifier  of his knowledge. More formally:
of his knowledge. More formally: 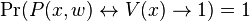
- Validity: Validity requires that the success probability of a knowledge extractor
 in extracting the witness, given oracle access to a possibly malicious prover
in extracting the witness, given oracle access to a possibly malicious prover  , must be at least as high as the success probability of the prover
, must be at least as high as the success probability of the prover  in convincing the verifier. This Property guarantees that no prover that doesn't know the witness can succeed in convincing the verifier.
in convincing the verifier. This Property guarantees that no prover that doesn't know the witness can succeed in convincing the verifier.
Details on the definition
This is a more rigorous definition of Validity:[2]
Let  be a witness relation,
be a witness relation,  the set of all witnesses for public value
the set of all witnesses for public value  , and
, and  the knowledge error.
A proof of knowledge is
the knowledge error.
A proof of knowledge is  -valid if there exists a polynomial-time machine
-valid if there exists a polynomial-time machine  , given oracle access to
, given oracle access to  , such that for every
, such that for every  , it is the case that
, it is the case that 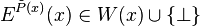 and
and 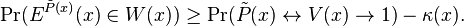
The result  signifies that the Turing machine
signifies that the Turing machine  did not come to a conclusion.
did not come to a conclusion.
The knowledge error  denotes the probability that the verifier
denotes the probability that the verifier  might accept
might accept  , even though the prover does in fact not know a witness
, even though the prover does in fact not know a witness  . The knowledge extractor
. The knowledge extractor  is used to express what is meant by the knowledge of a Turing machine. If
is used to express what is meant by the knowledge of a Turing machine. If  can extract
can extract  from
from  , we say that
, we say that  knows the value of
knows the value of  .
.
This definition of the validity property is a combination of the validity and strong validity properties in.[2] For small knowledge errors  , such as e.g.
, such as e.g.  or
or  it can be seen as being stronger than the soundness of ordinary interactive proofs.
it can be seen as being stronger than the soundness of ordinary interactive proofs.
Relation to general interactive proofs
In order to define a specific proof of knowledge, one need not only define the language, but also the witnesses the verifier should know. In some cases proving membership in a language may be easy, while computing a specific witness may be hard. This is best explained using an example:
Let  be a cyclic group with generator
be a cyclic group with generator  in which solving the discrete logarithm problem is believed to be hard. Deciding membership of the language
in which solving the discrete logarithm problem is believed to be hard. Deciding membership of the language  is trivial, as every
is trivial, as every  is in
is in  . However, finding the witness
. However, finding the witness  such that
such that  holds corresponds to solving the discrete logarithm problem.
holds corresponds to solving the discrete logarithm problem.
Protocols
Schnorr protocol
One of the simplest and frequently used proofs of knowledge, the proof of knowledge of a discrete logarithm, is due to Schnorr.[3] The protocol is defined for a cyclic group  of order
of order  with generator
with generator  .
.
In order to prove knowledge of  , the prover interacts with the verifier as follows:
, the prover interacts with the verifier as follows:
- In the first round the prover commits herself to randomness
 ; therefore the first message
; therefore the first message  is also called commitment.
is also called commitment. - The verifier replies with a challenge
 chosen at random.
chosen at random. - After receiving
 , the prover sends the third and last message (the response)
, the prover sends the third and last message (the response)  .
.
The verifier accepts, if  .
.
Sigma protocols
Protocols which have the above three-move structure (commitment, challenge and response) are called sigma protocols. The Greek letter  visualizes the flow of the protocol. Sigma protocols exist for proving various statements, such as those pertaining to discrete logarithms. Using these proofs, the prover can not only prove the knowledge of the discrete logarithm, but also that the discrete logarithm is of a specific form. For instance, it is possible to prove that two logarithms of
visualizes the flow of the protocol. Sigma protocols exist for proving various statements, such as those pertaining to discrete logarithms. Using these proofs, the prover can not only prove the knowledge of the discrete logarithm, but also that the discrete logarithm is of a specific form. For instance, it is possible to prove that two logarithms of  and
and  with respect to bases
with respect to bases  and
and  are equal or fulfill some other linear relation. For a and b elements of
are equal or fulfill some other linear relation. For a and b elements of  , we say that the prover proves knowledge of
, we say that the prover proves knowledge of  and
and  such that
such that 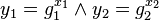 and
and 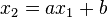 . Equality corresponds to the special case where a = 1 and b = 0. As
. Equality corresponds to the special case where a = 1 and b = 0. As  can be trivially computed from
can be trivially computed from  this is equivalent to proving knowledge of an x such that
this is equivalent to proving knowledge of an x such that  .
.
This is the intuition behind the following notation, which is commonly used to express what exactly is proven by a proof of knowledge.
states that the prover knows an x that fulfills the relation above.
Applications
Proofs of knowledge are useful tool for the construction of identification protocols, and in their non-interactive variant, signature schemes. Such schemes are:
They are also used in the construction of group signature and anonymous digital credential systems.
See also
- Cryptographic protocol
- Zero-knowledge proof
- interactive proof system
- Topics in cryptography
- Zero-knowledge password proof
- Soundness (interactive proof)
References
- ↑ Shafi Goldwasser, Silvio Micali, and Charles Rackoff. The knowledge complexity of interactive proof-systems. Proceedings of 17th Symposium on the Theory of Computation, Providence, Rhode Island. 1985. Draft. Extended abstract
- 1 2 Mihir Bellare, Oded Goldreich: On Defining Proofs of Knowledge. CRYPTO 1992: 390–420
- ↑ C P Schnorr, Efficient identification and signatures for smart cards, in G Brassard, ed. Advances in Cryptology – Crypto '89, 239–252, Springer-Verlag, 1990. Lecture Notes in Computer Science, nr 435